## Why Air Gapping is Critical for Private Key Security
In today’s digital landscape, private keys are the ultimate guardians of your cryptocurrency, sensitive data, and digital identity. These cryptographic strings unlock access to your most valuable assets – making them prime targets for hackers. Air gapping provides the strongest defense by creating physical isolation between your private key and any network-connected device. This guide walks you through implementing air-gapped security step by step, ensuring your keys remain impervious to remote attacks.
## Understanding Air-Gapped Systems
An air-gapped system is a computer or device completely disconnected from all networks:
– **Zero connectivity**: No internet, Bluetooth, Wi-Fi, or cellular access
– **Physical isolation**: Stored in a secure location without peripheral connections
– **Attack surface reduction**: Eliminates 99% of remote hacking vectors
Unlike “cold storage” which may occasionally connect, true air gapping maintains permanent offline status. This makes it immune to malware, phishing, and remote exploitation.
## Step-by-Step: Creating Your Air-Gapped Private Key
### Step 1: Prepare Your Air-Gapped Environment
1. Select a clean device: Use a brand-new or factory-reset computer (e.g., Raspberry Pi or old laptop)
2. Remove networking hardware: Physically disconnect Wi-Fi cards and Ethernet ports
3. Verify isolation: Boot using a Linux live USB (like Tails OS) to ensure no background connections
### Step 2: Generate Keys Offline
1. Install offline tools: Load cryptographic software via USB (e.g., GnuPG, Electrum for crypto)
2. Create keys: Run key generation commands while offline
“`
gpg –gen-key # For PGP keys
“`
3. Disable swap files: Prevent key material from being written to disk
### Step 3: Secure Storage Methods
– **Metal backups**: Engrave keys on cryptosteel plates (fire/water resistant)
– **Encrypted USBs**: Use VeraCrypt to create encrypted volumes (store in bank vaults)
– **Paper wallets**: Print QR codes with tamper-evident bags (store in multiple locations)
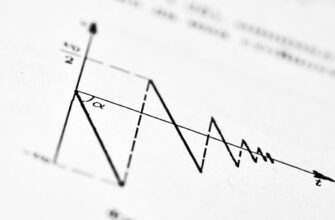
### Step 4: Transaction Signing Protocol
1. Create unsigned transaction on online device
2. Transfer via QR code or USB to air-gapped machine
3. Sign transaction offline
4. Broadcast signed transaction using online device
## Air Gapping Best Practices
– **Physical security**: Store devices in fireproof safes with biometric locks
– **Multi-sig setups**: Require keys from 2+ air-gapped devices for critical operations
– **Regular audits**: Verify backup integrity every 6 months
– **Zero-exception policy**: Never connect USB devices without malware scanning first
## Frequently Asked Questions (FAQ)
**Q: Can air-gapped systems still be hacked?**
A: Only through physical access or compromised supply chains. Mitigate with tamper-evident seals and trusted hardware sources.
**Q: How often should I update air-gapped software?**
A: Update offline tools annually via verified USB transfers. Never connect to download updates.
**Q: Is a hardware wallet considered air-gapped?**
A: Only dedicated devices like ColdCard or Passport provide true air gapping. Avoid “hybrid” wallets with Bluetooth/USB connectivity.
**Q: What’s the biggest mistake in air gapping?**
A: Using the same device for online activities pre-configuration. Always start with factory-fresh hardware.
**Q: Can I recover keys if my air-gapped device fails?**
A: Yes – if you maintain encrypted offline backups in multiple geographic locations. Test restoration annually.
## Final Security Considerations
Air gapping remains the gold standard for private key protection, but requires disciplined execution. By following these steps, you create an impenetrable barrier against remote threats. Remember: The inconvenience of air gapping pales in comparison to losing life-changing assets. Treat your private keys like nuclear codes – because in the digital world, they are.